
With an estimated 55.5 million users, smartphones are all but ubiquitous in the UK, with 96% of those aged between 16 – 34 and 91% of those aged between 35 – 54 owning a device. Changing phones, or upgrading contracts is relatively straightforward, and consumers can transfer all their data during this process. To legitimately undertake this process, you need to notify your mobile operator provider, providing your Mobile Identification Number (MIN) and obtaining a Porting Authorisation Code (PAC). This transfer is called a Subscriber Identity Module (SIM) Swap.
It is estimated that more than 50,000 legitimate SIM-swaps occur every day. Unfortunately, this volume of transactions attracts fraudsters, who can easily hide in the background.
Unsurprisingly, being able to take over a mobile phone, as a way of undertaking account takeover on numerous types of accounts e.g., banking, is an attractive prospect. The easiest way to take ownership of a SIM is to fool its associated mobile provider into believing that the authorised account holder is making a genuine request. Numerous techniques to obtain log-in credentials for operators exist, including spoof log-in portals, which would then steal credentials. See below for an example impersonation of Verizon. Mentioned in our previous article, details could also be purchased on the dark web.

Another way to steal credentials is to physically impersonate a victim. As part of my investigation, I interviewed a reformed fraudster, who recanted his personal experience with SIM swap fraud.
‘I started on a small scale, selecting victims whose details and phone number I already knew. I then obtained a forged driving licence and utility bill before visiting a store to buy a handset. With this new handset I would do a SIM swap, porting my victim’s data onto it, and into my possession’.
Though this approach is limited, as he would look aesthetically like that of his victim, he added that he would often ‘find out who worked in the store and research them beforehand; offering a bribe or finding information which I could later blackmail them with’.
With the COVID-19 pandemic on-going this has thankfully stopped this approach. However, another interviewee admitted that it ‘was not a problem’. This former cybercriminal admitted that organised gangs conduct extremely thorough research on network operators, testing systems and obtaining policies for the issuing of PAC’s and MIN’s. Information on companies (whether they are easy to crack or not) is readily available on the dark web. He continued to explain that through ‘spoof’ messages to customers or contacting providers and utilising previously obtained information about company policies (e.g., what security checks are favoured) fraudsters have adapted quickly, and effectively.
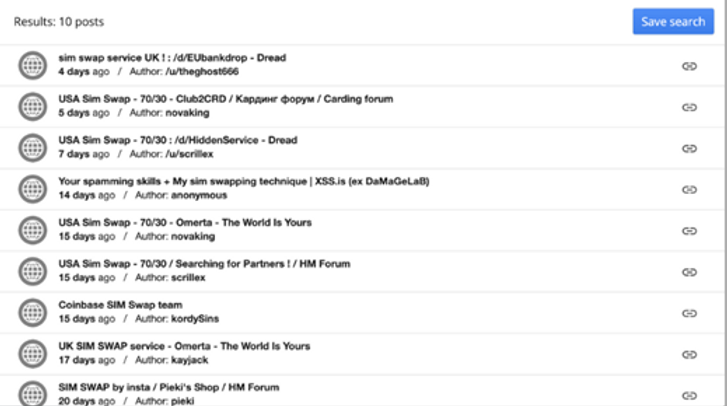
In a recent study by Princeton University, it was estimated that 4 / 5 SIM swap fraud attempts are successful. Having asked a specialist colleague to investigate this on the dark web, over a period of 15 days they found the following adverts.
The level of research and organisation undertaken by cybercriminals is clearly underestimated. As are the pieces of information that could enable them to swap your SIM.
So, what are they after?
– Personal and Work email account information (to intercept 2FA)
– Text messages (to intercept 2FA)
– Bank account / credit card account information
– Access to bitcoin and other cryptocurrency wallets
– Apple Pay / PayPal account details
– Other personal information, e.g., secret question, preferred password, D.O.B
As reliance on smartphones has increased, now Is the time to check your security measures, and those of your family, friends, colleagues, staff, and customers.
Contact Phronesis Technologies today to discuss their specific SIM swap fraud detection services – they can ensure that, in real time, the SIM and device ID is as expected and that no porting or call-forwarding settings have been activated. They can also check other personal details e.g., address is correct.
Peter Taylor is an accomplished and distinguished fraud expert and investigator. He begun his career with Greater Manchester Police, before obtaining the position of Head of Fraud for Major Loss Adjusters. Since founding a consultancy firm, Peter has expanded his areas of expertise and is a cross-industry specialist in and cybercrime and counter-fraud measures.
As Phronesis continues to expand, now offering our Mobile Identity and Fraud Prevention services directly to enterprise, we wanted to commission research into cybercrime, and the many facets within, to both add to our understanding, and to share with our growing network of partners, clients, followers, and of course, to those who generally operate in the sector.
Edits and afterword by Toni Pickering
References:
Four-fifths of SIM-swap fraud attempts successful (computerweekly.com)
Last updated on March 28, 2024


We provide comprehensive device, network and mobile numbering data available.
Contact us > Chat to an expert >